Over 787,000 Apps On Google And Apple Stores Do Not Have Privacy Policy.
The latest App Store security report says many apps in Apple’s App Store lack privacy details. After analyzing 5 million apps, the report says they found no privacy details in 10% of apps. Only 10% of the 5 million apps analyzed contain privacy data. The report was published by Pixalate, a fraud protection company. The […]
These 8 Malware Infected Android Apps Will Affect Your Data; here you can find a list of Android malware apps

Maxime Ingrao said the malware, called Autolycus, was present in at least eight Android apps that had more than three million downloads. French security researcher Maxime Ingrao is warning Android users about a new family of malware that subscribes to premium services. It said the malware, called Autolycus, was found in at least eight Android […]
Pokemon Go developer Niantic has launched its Campfire social network
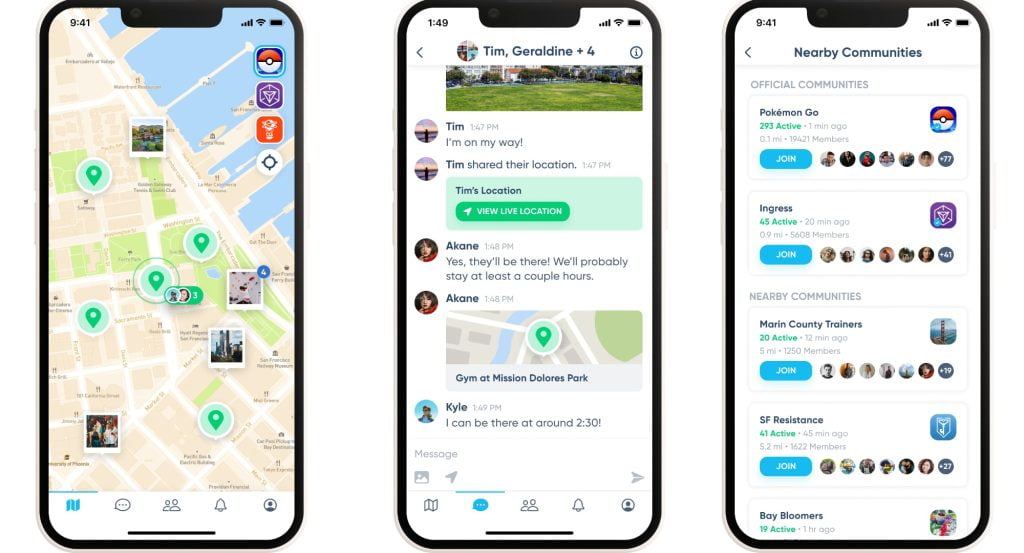
Pokemon Go creator Niantic is developing a social app for its games — and it’s coming soon. The developer says the app, called Campfire, will begin its global launch “in the coming days.” The campfire was originally announced in May and has been in testing with Ingress players for the past few months. The first […]
Match Group brings free Tinder background checks to other dating apps
Match Group is bringing Tinder’s free background check to two of its other dating apps: Match (formerly Match.com) and Stir, a single-parent dating site (via CNBC). The system works similarly to Tinder: people can use it to see who they’re talking to or planning to meet, it has a history of “violent and harmful behavior”, […]
High-flying experiment: Do stem cells grow better in space?
High-flying experiment: can stem cells grow better in space? Scientists are investigating whether stem cells can grow faster in a zero-gravity environment by sending their own stem cells into space. Stem cell therapies may be used to treat various diseases in the future. Researcher Dhruv Sareen’s own stem cells are now circulating on Earth. Mission? […]
How China became ground zero for the auto chip shortage
How China Became the Basis for Car Chip Shortages Although China is the world’s largest automaker and leader in electric vehicles (EVs), it relies on imports from Europe, the United States, and Taiwan for almost all of its chips. From his small Singaporean office, Kelvin Pang is ready to bet a $23 million salary won’t […]
Twitter calls Musk’s bots complaints ‘irrelevant sideshow’
Twitter calls Musk’s bot complaints an ‘irrelevant sideshow’ Twitter Inc. denied Elon Musk’s complaints that he didn’t have enough information about spam and bot accounts that were “irrelevant sideshows” and urged a judge to try to overturn his $44 billion purchase as soon as possible. “The earliest possible trial date is needed,” Twitter lawyers said […]
India May Enact Regulations Asking Big Tech to Compensate News Outlets for Their Content
India may set regulations that will require Big Tech to pay news channels for their content aceAustralia’s “News Media and Digital Platforms Mandatory Bargaining Code” obliges Big Tech companies to pay news publishers to display links on their platforms. Implementation of the system is being explored worldwide and India is likely to consider a similar […]
After Deepest, Clearest Images Of Universe, James Webb Telescope Treats Us With Detailed Images Of Jupiter
After the deepest and clearest images of the universe, we treat the James Webb telescope with close-up images of Jupiter Last week, NASA’s James Webb Space Telescope showed us the most detailed pictures of the universe that humans have ever seen. The out-of-this-world (literally) images from the James Webb Space Telescope are amazing, and today […]
Indian Cyber Agency Warns About Multiple Bugs in VMware Products
India’s cyber agency warns of more flaws in VMware products The Indian Computer Emergency Response Team (CERT-In) has issued new warnings to users, this time reporting various vulnerabilities in the products of enterprise cloud service provider VMware. CERT-In found flaws in VMware ESXi and Cloud Foundation that could allow an attacker to gain access to […]